Blog
Insights, Trends & Solutions from the World of IT

This Is How Kids Get Into Trouble Online
Here’s the truth about online risks for kids. They don’t show up when you’re sitting right there beside them. They show up the moment you’re…

When Employees Become the Weak Link
Hackers don’t need to outsmart your firewall. They just need one employee to slip up. A careless click. A reused password. A little too much…
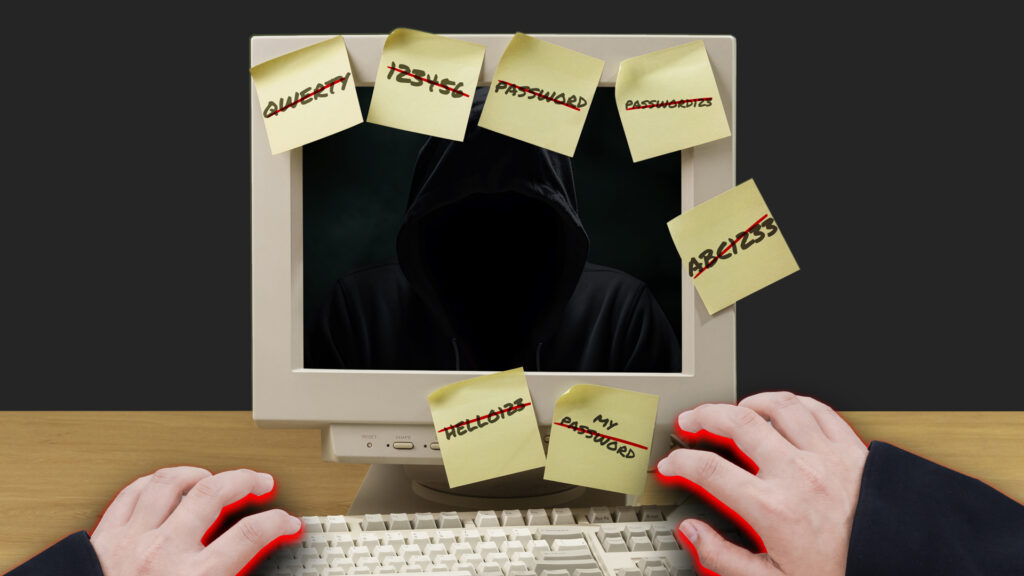
The Internet’s Worst Habit
Every year the list of most common passwords makes the rounds online, and every year it’s the same bad news. People are still using “123456”…

Guess Who’s Already Inside
Your phone is more than a phone. It is a wallet, a filing cabinet, a work desk, and a personal vault and hackers know it….

You’re Wasting Power You Don’t See
Here’s the thing nobody thinks about:The internet isn’t some invisible, weightless cloud. It’s power-hungry. If the internet were a country, it would rank among the…

The Free Wi-Fi Lie
Let’s be real: free Wi-Fi feels like a gift.Airports, hotels, coffee shops.. it’s everywhere. You tap, you connect, you’re online. Easy. But here’s the truth….

This Is How You Kill Productivity
Here’s the thing about clutter: it’s never just about the closet, the garage, or the spare room. Clutter creeps into your business too, inside the…

The Next Big Threat Waiting at Your Digital Door
Businesses today are facing a ransomware threat that is more aggressive and damaging than anything seen before. Every week, organizations discover their systems locked, their…

How Hackers Cash In on Your Loneliness
Online dating has changed the game, sure. But let’s not kid ourselves, the internet is full of predators. You swipe, you match, you think you’ve…

The Remote Work Security Gap No One Talks About
Remote work has been a game-changer. Lower overhead. Happier employees. Wider talent pool. All wins. But there’s a catch: every remote login, home Wi-Fi network,…